Cloning is the process of creating a replica of a computer’s files to another device. The replica includes system files, apps and programs, settings, and other stored data, such as documents, images, audio, or video. The technique can reduce downtime when migrating systems and protect against sudden data loss. Many power users and IT departments favor clones to secure important data for that reason.
However, you do not need any special skills to clone a laptop and enjoy its benefits. While cloning might seem complex, it is typically straightforward and saves time after a hardware failure or upgrade.
This step-by-step guide explains how to clone your laptop to an external drive on Windows and macOS.
Key Takeaways:
What Is Disk Cloning?
Disk cloning produces a bit-by-bit copy of a storage device on different media. A bit is the smallest unit of digital data in a storage device. This comprehensive approach allows the new drive to function exactly like the original one. That means replacing a failed or outdated laptop takes less time than ever.
Top Reasons Why You Should Clone Your Laptop
Having a recently cloned drive is useful for several reasons. The cloning process will vary between people depending on their needs and usage.
For everyday users, a clone is the easiest method of system migration after buying a new laptop. They can also serve as backups in the event of an unexpected failure.
Enthusiasts might turn to clones for archives because they preserve the whole system at a specific point in time.
Corporate IT can even deploy a standard clone for consistent installations across multiple computers within the company.
Regardless, cloning is not for everyone. As an example, using clones to regularly archive and restore data requires more storage space. The increased overhead might not be worth it from a cost perspective. Carefully assess your situation to decide if cloning makes the most sense.
Essential Tools and Tips for Cloning
In most cases, people use cloning software to save the contents of their laptop to an external drive. There are many programs available on Windows and macOS. Users should select the software that best fits their budget, experience level, and needs. For casual users, a free tool that is easy to use is usually the smartest choice. Other users demand more robust features, so a premium option is worth it.
Software is not the only thing you will need to clone your laptop. Most laptops now have solid-state drives (SSDs) instead of hard disk drives (HDDs). Many models have SSDs that transfer data over a Serial ATA (SATA) interface. However, they often lack a SATA port for external drives. Therefore, you will likely need an adapter or enclosure. These components convert the SATA interface of the internal drive to the USB interface of the external drive.
Here is a full list of essential tools to clone your laptop:
- Cloning software or built-in utility
- A formatted external drive
- USB to SATA adapter or enclosure
- Stable power supply
Note: If your laptop contains an M.2 SSD, you will need a NVMe to USB adapter instead.
In addition, decluttering the source device (the one being cloned) can improve the performance of the destination drive.
There are a few more factors to consider when cloning.
Choosing the Right External Drive
You should choose an external drive based on the following criteria:
- Storage Capacity: Ensure that the device has enough space to hold all of your laptop’s files.
- HDD vs. SSD: An external hard drive has a lower cost per gigabyte of storage. It is excellent for cases where high speeds are not required. An external SSD is a better choice for people who need faster data transfer, such as a bootable backup.
- Compatibility: The external device should work with the laptop’s connections and file system.
- Size: Use a portable hard drive or SSD if you will need to frequently transport the device between places.
Our SecureDrive® products are a great option for users who want another layer of data protection for their external HDD. These encrypted external drives provide security features like keypad and phone authentication to prevent unauthorized access. They are ideal for people who intend to keep a copy of their laptop’s contents or transport the external drive. The hardware encryption safeguards stored data in the event of device loss or theft.
Note: You must format a new external hard drive with Disk Management (Windows) or Disk Utility (macOS) before beginning.
Create Backup Before Cloning
Do not start the cloning process before backing up stored data.
Cloning software is safe and reliable, but errors leading to data loss can happen. A recent backup safeguards against accidental deletion, file corruption due to an abrupt interruption, and uncommon bugs or conflicts. This simple step preserves the laptop’s previous setup and offers some redundancy for hardware, software, or human error.
Advanced Cloning Techniques
Cloning a laptop is a direct process. Still, users can adjust it to suit their needs or avoid duplication.
These specialized methods can enhance or streamline efforts:
- Scheduled Cloning: Automates the process to occur at regular intervals.
- Incremental Cloning: Saves copies of changed data since the last clone.
- Differential Cloning: Saves copies of changed data since the last full clone.
- Dual-Boot Cloning: Ensures both operating systems remain functional and partitioned after cloning.
- Multicast Cloning: Copies a source drive to multiple target drives at once.
In most instances, a home user will not benefit from advanced techniques when cloning their laptop’s drive.
Those with Windows 10 and 11 can create a system image within the Control Panel. This option is found under the System and Security field as Backup and Restore (Windows 7). Microsoft’s built-in tool creates a snapshot of your system, which differs slightly from a clone. It cannot resize partitions, compress files, or migrate data to a mismatched drive.
As a result, we recommend using dedicated cloning software.
Fortunately, Windows 11 and 10 has plenty of options in terms of cloning tools.
Acronis True Image
Acronis True Image includes a suite of security and system maintenance tools. It is a popular choice for disk cloning or data backups due to its clean interface and advanced capabilities. Its downside is that it costs $50 for an annual subscription. Cloning features are locked during the 30-day trial.
To clone a laptop using Acronis True Image:
- Open the program.
- Select Tools from the left sidebar and then Clone Disk.
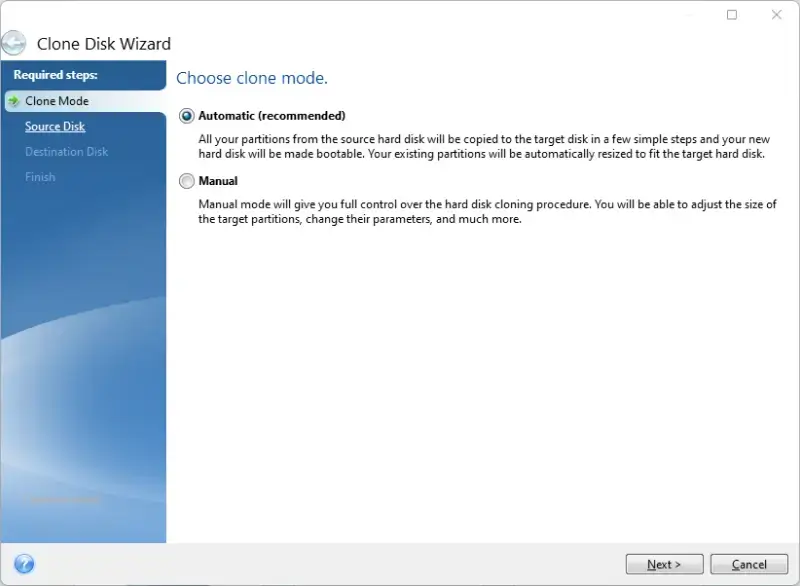
- Choose Automatic or Manual on the Clone Mode screen. We suggest Automatic for most users.
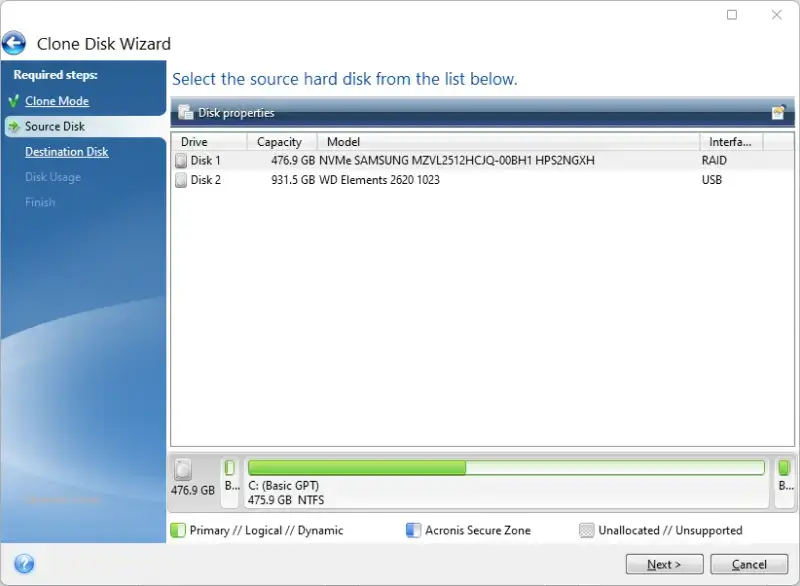
- Select the laptop’s drive from the Source Disk screen.
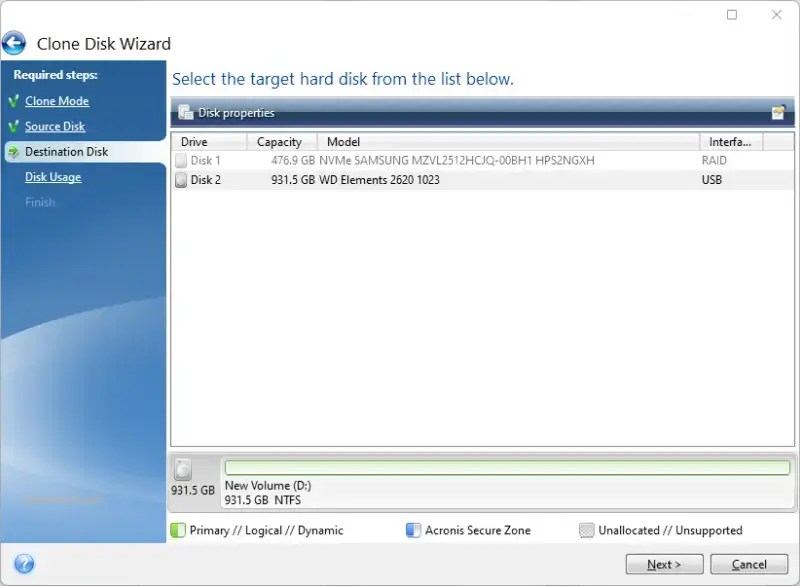
- Select the external drive from the Destination Disk screen.
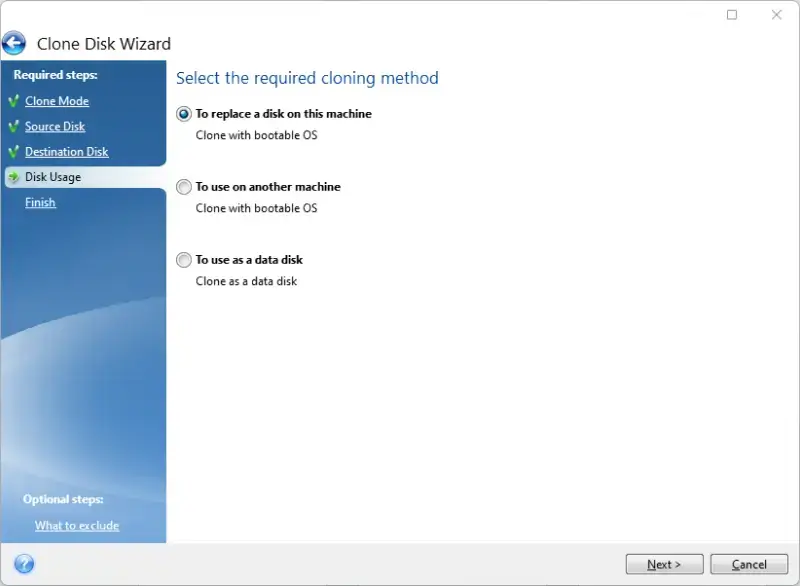
- Choose the desired method from the Disk Usage screen. To replace a disk on this machine is best for swapping drives in the same device. To use on another machine is best for migrating files to another device. To use as a data disk is best for backups.
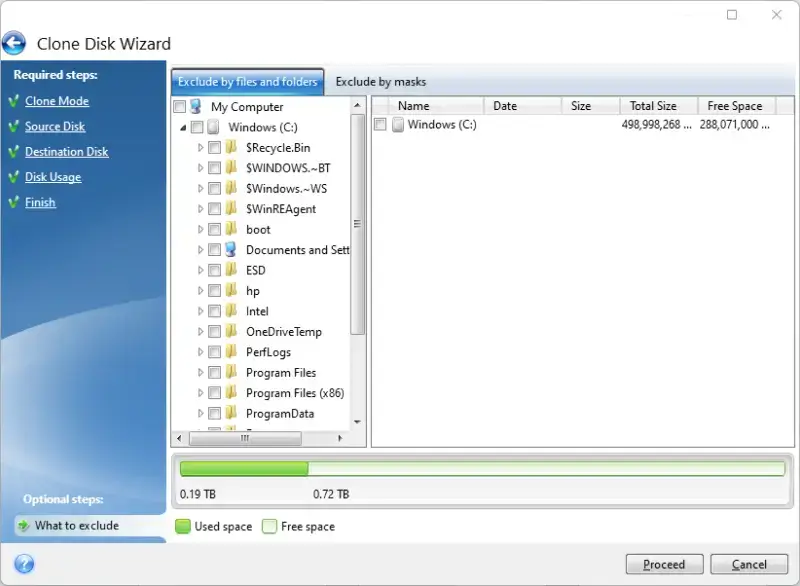
- Click What to exclude in the bottom-left corner of the screen to omit files and folders from the clone. Skip this step if you want a complete clone.
- Click Proceed to start the cloning process.
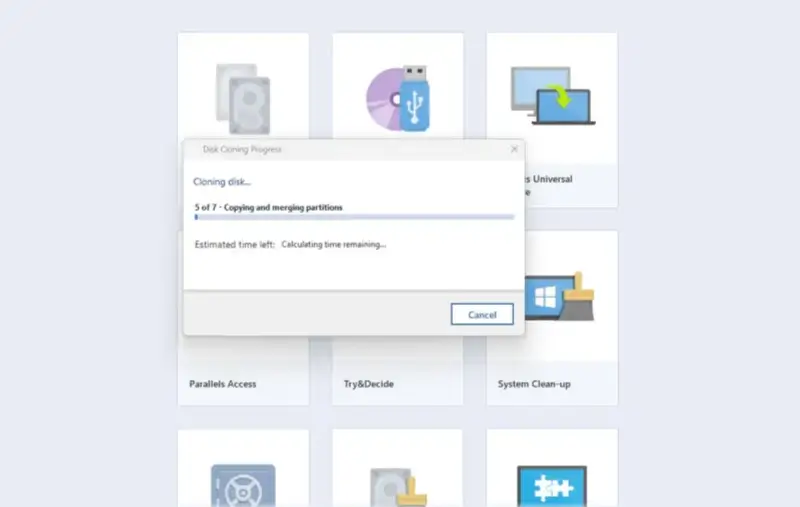
- The system will notify you of the next steps when it finishes cloning the laptop.
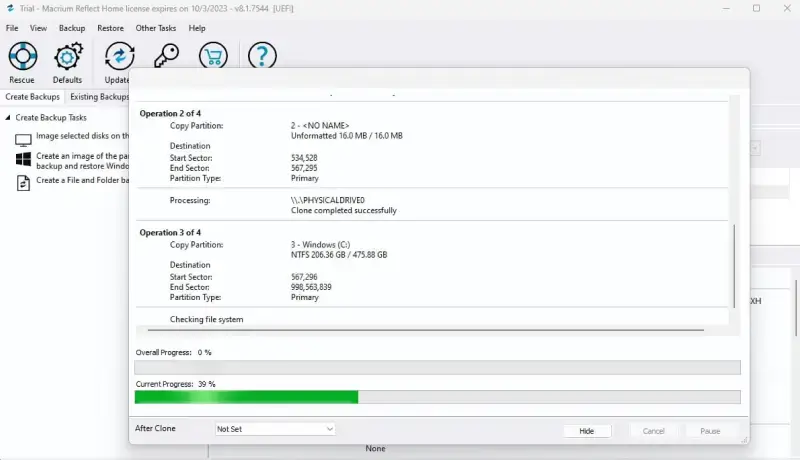
Macrium Reflect
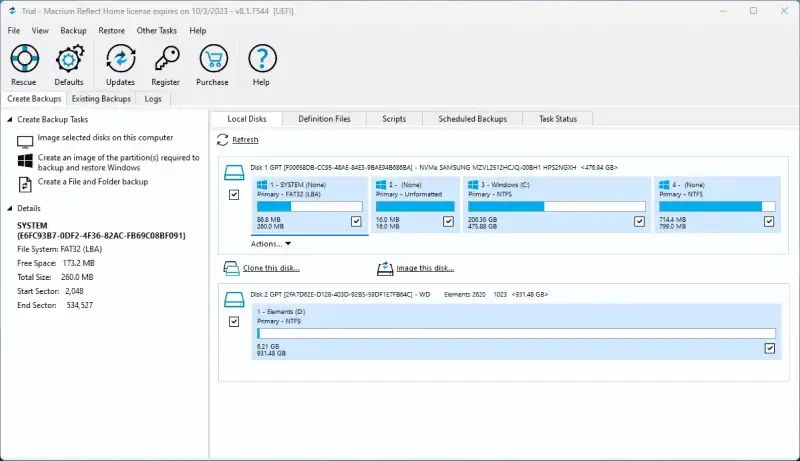
Macrium Reflect is another option for users who want to clone a laptop with user-friendly software. It has a 30-day free trial with access to the cloning tool.
To clone a laptop using Macrium Reflect:
- Open the program.
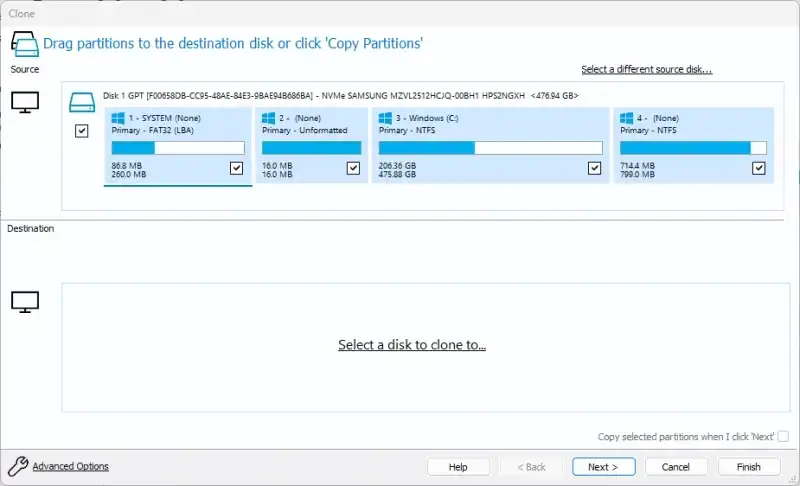
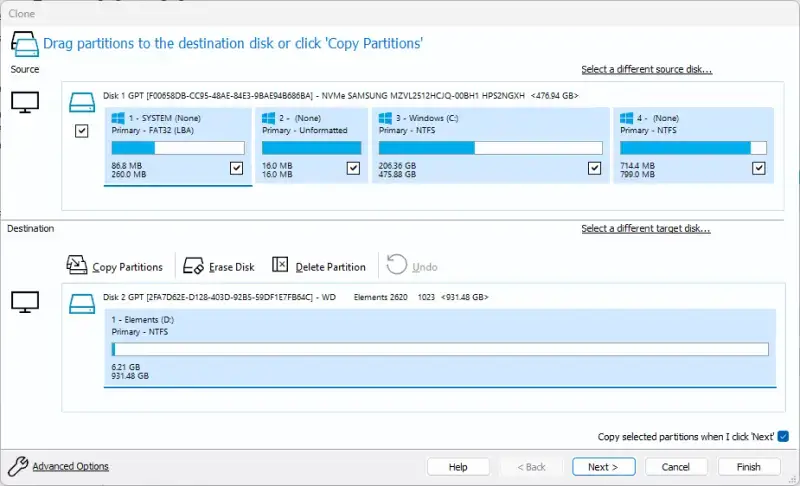
- Select Clone this disk… for the laptop’s system drive.
- Click Select a disk to clone to… on the Clone screen to choose the external drive. Confirm that it has enough storage space to hold the clone.
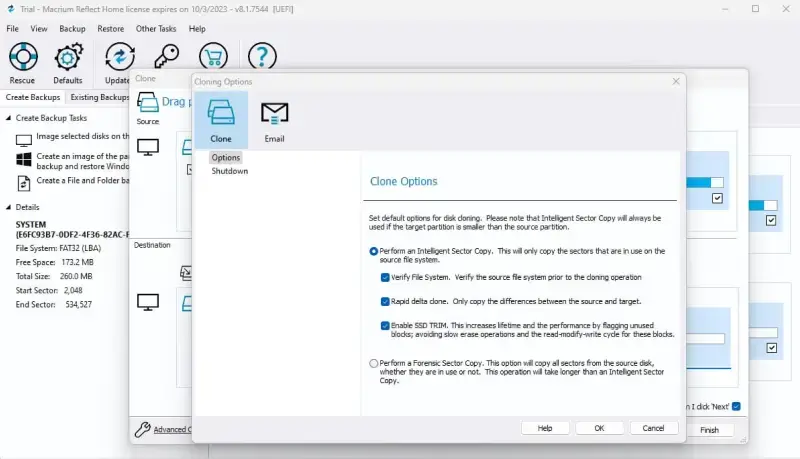
- Click Advanced Options in the bottom-left corner of the Clone screen to customize settings. Skip this step if you want a basic clone.
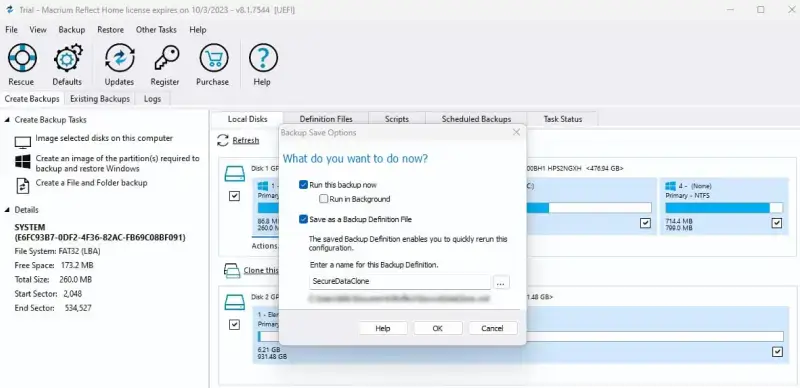
- Click Next.
- Follow the on-screen instructions to adjust save options if desired.
- Click OK to begin.
- The software will report its progress throughout the cloning process.
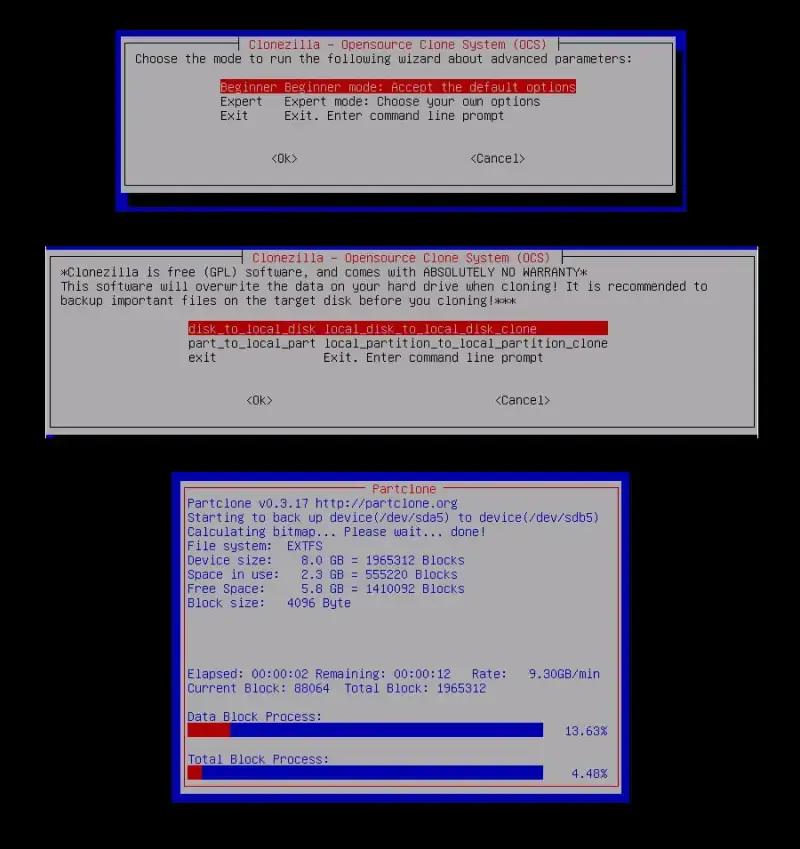
Clonezilla
Clonezilla is free, open-source software for disk imaging and cloning. It is tailored toward experienced users who want rich features without a license or subscription. Clonezilla supports dozens of file systems, partition options, and multicast cloning for up to 40 devices. However, the program runs on a lightweight Linux distribution, often accessed off a bootable USB. The setup and steep learning curve makes Clonezilla a niche choice.
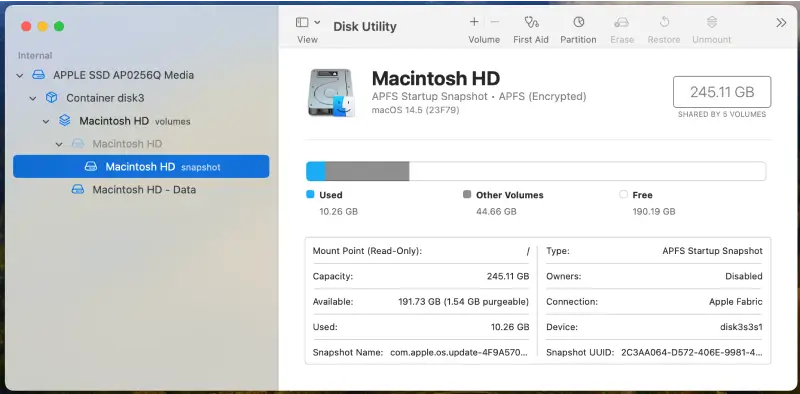
Unlike Windows, macOS has a system utility that allows users to duplicate their Mac’s drive. This means you do not need to download anything in order to clone your MacBook. Although, some third-party software may offer more functions.
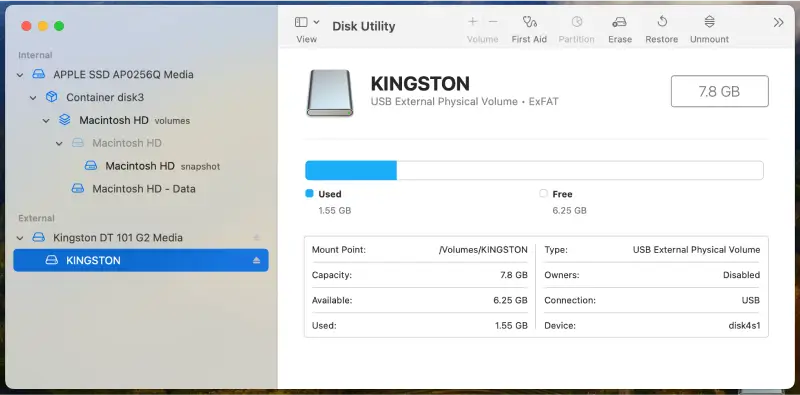
Disk Utility
Disk Utility requires some manual input and lacks advanced cloning techniques, but it is more than capable as a one-time option.
To clone a MacBook using Disk Utility:
- Type Disk Utility in Spotlight.
- Select the MacBook’s internal drive from the sidebar.
- Click the Restore tab.
- Choose the external device as the destination drive.
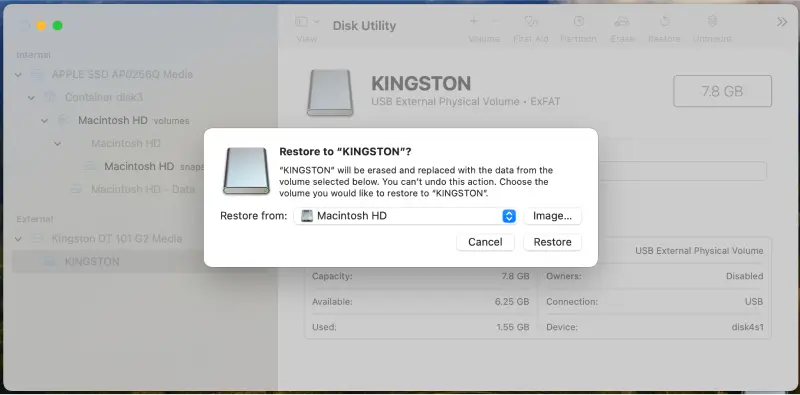
- Click the Restore button on the toolbar.
- Select the internal drive from the Restore From dropdown menu.
- Select the external drive from the Restore To drop down menu.
- Click Restore.
Testing Your Cloned Drive
You need to verify the cloned drive is intact and bootable once finished. Follow these easy steps to test and troubleshoot your device.
Step 1: Check the Clone
Open File Explorer (Windows) or Finder (macOS) and compare the external drive to the laptop. Confirm that all files, folders, and programs are present and located in the right place. Next, view the drive’s properties. Ensure the partition structure and used space of the external HDD or SSD matches the laptop.
Step 2: Boot From the External Drive
Shut down the laptop and attempt to boot from the connected drive by pressing a certain key during startup.
To access the boot menu and start from an external drive:
- Windows: Press Esc, F12, or another function key to enter the boot menu and select the external drive from the list.
- Mac: Press and hold the Option key (⌥) until Startup Manager appears, then change the boot order by choosing the external drive.
Step 3: Test the System
Open the most critical apps to see if they work as intended. In addition, confirm that all system settings and preferences were transferred. Note any errors or unusual behavior during the test. This could indicate a serious issue with the clone.
Troubleshooting Common Issues
Sometimes a cloned disk fails to initialize. In these cases, you may need to repair the bootloader. The bootloader is a small string of code that locates the operating system and performs basic hardware checks. If the bootloader did not copy correctly while cloning, then the external drive will not launch. That often means repairing Windows boot issues with the Startup Repair tool or fixing the install within macOS Recovery mode.
You should also verify that the right partition is active on Windows. On Macs, make sure the startup disk is configured.
If problems persist, consider re-cloning the laptop to the external drive.
SecureData is a leading provider of data security solutions. From storage products and software to professional data recovery services, our experts can help you throughout the cloning process. Don’t just trust anyone with your sensitive data. Trust an experienced team with a history of results.
Contact us to speak with our support staff today.
Frequently Asked Questions
How do I copy my laptop to an external hard drive?
You can copy your laptop’s contents to an external drive using cloning software. The ideal tool depends on your personal needs.
What is the difference between a clone and backup?
A clone is a bit-by-bit replica of the source drive. A backup is a copy of selected files from the source drive. Clones are better suited for archiving data and migrating systems while backups preserve important files.
Can I clone my laptop to a larger or smaller external drive?
It depends. Some cloning software lets users copy their laptop to an external drive of a different size. However, resizing partitions is a more advanced feature.
Does cloning overwrite data on the destination drive?
Yes. Be sure to back up essential data stored on the external drive before cloning the laptop.
How long is the cloning process?
The duration of the cloning process varies based on the amount of data on the laptop.
Does Windows or macOS come with a cloning tool?
While Windows 10 and 11 allows users to create a system image, it does not have an optimized cloning tool. People with macOS can use Disk Utility to copy their MacBook’s system drive to another device.