Microsoft Access is a user-friendly database management system. The valuable tool allows individuals and organizations to create and manipulate large amounts of data. However, corrupted Access tables can disrupt operations and prevent projects from being completed on time. SecureData, experts in file repair and recovery, developed specialized software to resolve corruption in Access and recover critical data.
How To Restore a Corrupted Access Table
Launched in 1992, Microsoft Access is an application in the Office 365 suite of products, designed for managing smaller-scale databases. Specifically, MS Access organizes and retrieves information through tables and data-related queries. Users have the freedom to build relationships between tables for analysis or create complex queries. Despite its robust features, it is often positioned as an accessible, versatile alternative to traditional database management systems. That accessibility and functionality makes the system a popular choice among users with varying levels of expertise. Thousands of businesses use Access for customer relationship, inventory, and project management.
The applications of Access highlight the impact of data loss. While the system is stable, hardware failure, malicious software, sudden shutdowns, network issues, exceeded limits, and unexpected glitches can corrupt Access files. Regardless of the reason, being offline can be devastating.
Fortunately, there is an efficient method for repairing corrupted files and restoring Access tables.
SecureRecovery for Access is a proven file repair solution that can reduce downtime and reverse data loss from corruption.
Install SecureRecovery for Access: Specialized File Repair Software
Available as a demo or licensed product, SecureRecovery for Access repairs corrupted .mdb files.
The file repair utility is compatible with the latest editions of the database management system and legacy versions. That means even .accdb and msaccess.exe formats are repairable and recoverable. For other file extensions, review our professional database data recovery services. Our technicians can often write custom scripts to locate proprietary or uncommon extensions.
The data recovery tool also functions on encrypted databases up to Access 2003.
At SecureData, we understand how important it is to repair extensive corruption and recover all available database elements. As a result, SecureRecovery for Access can restore tables, relationships between tables, links to external tables, queries, forms, reports, macros, indexes, modules, and counter fields.
Furthermore, SecureRecovery for Access comes with a Data Browser feature that retrieves specific items within a corrupted database.
The following step-by-step guide will assist you in quickly repairing corrupt files and restoring data with SecureRecovery for Access.
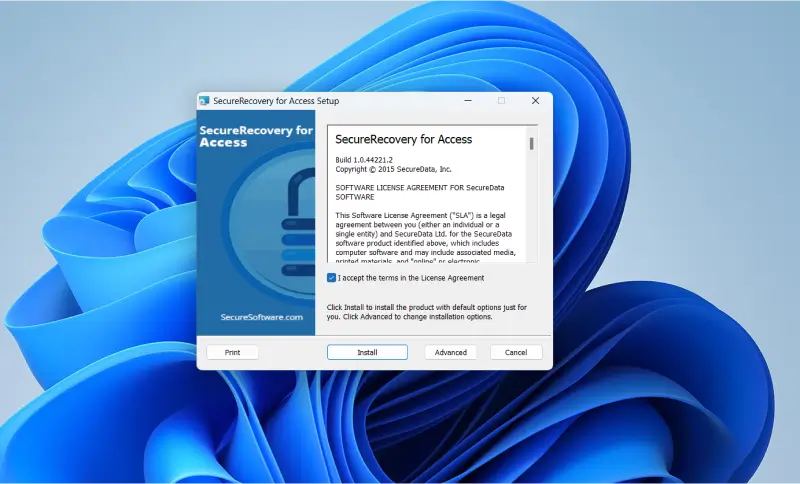
Step 1: Download and Install
- Download SecureRecovery for Access to start database repairs.
- Allow SecureRecovery for Access to make changes to your computer. This step permits the software to access the corrupt files.
- Read the Software License Agreement and click Install to continue.
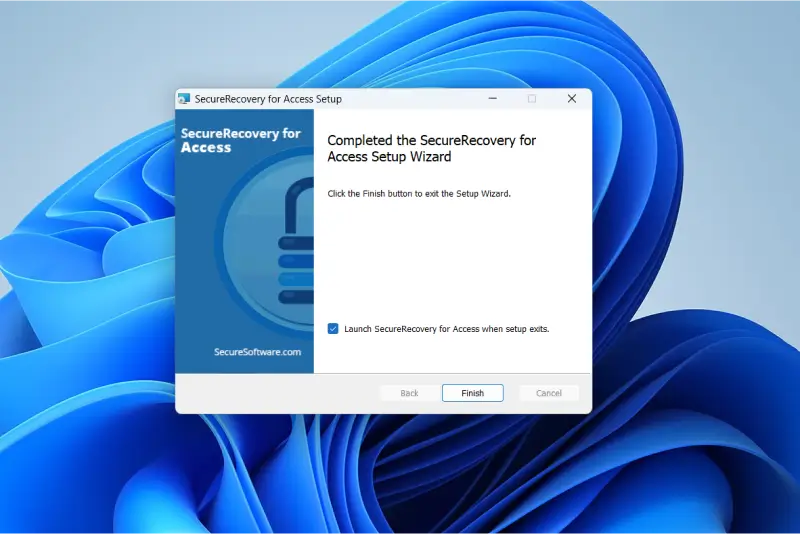
Step 2: Launch the Utility
- Once the installation is complete, enable the Launch SecureRecovery for Access checkbox and click Finish. If you want to delay the process, deselect the option and exit.
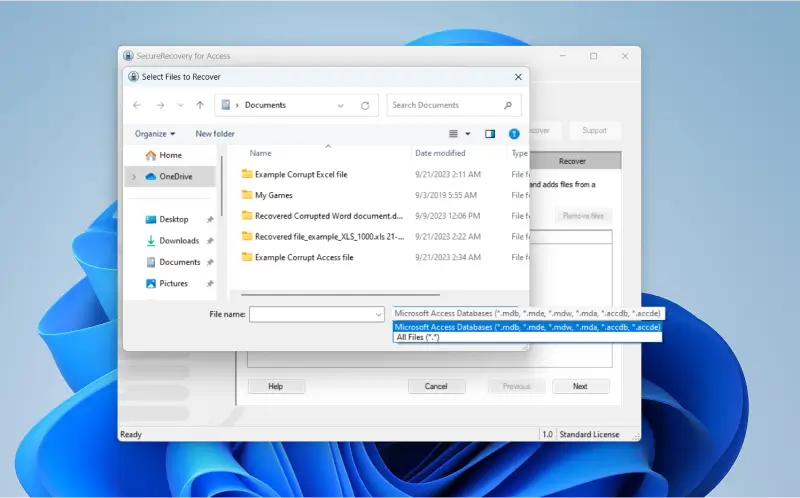
Step 3: Browse for Corrupt Access Files
- If you know exactly what you need, you can browse for specific files and repair corrupt data from the main screen of SecureRecovery for Access. Select Microsoft Access databases (*.mdb, *.mbe, *.mdw, *.mda, *.accdb, *.accde) in the file type drop-down menu.
- If you are using the demo, but have acquired a product key, you can open the Help menu and click License Manager. Input the product key. The manager will close once the license is accepted.
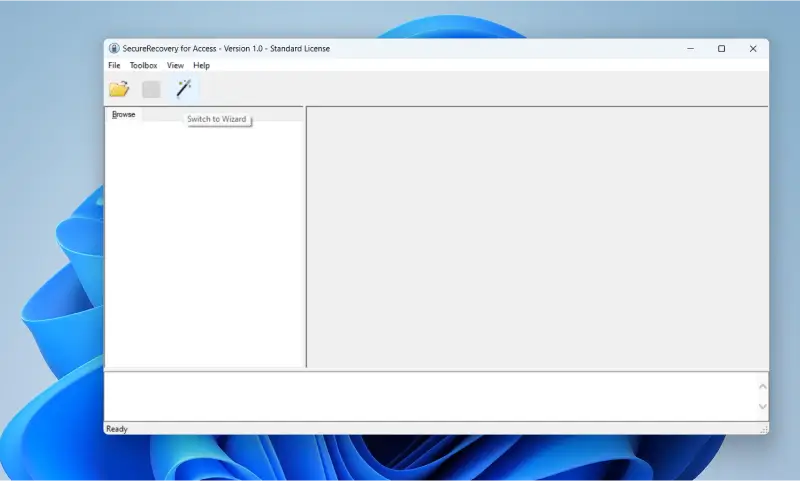
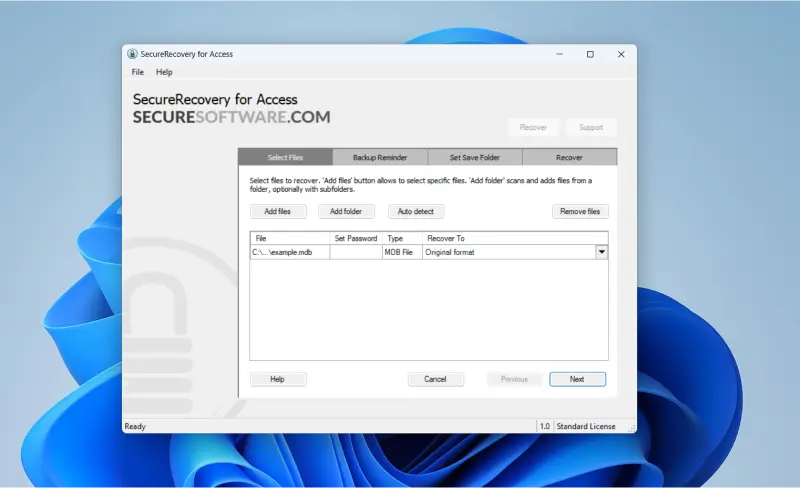
Step 4: Locate Corrupt Files with Wizard
- For those that want to simplify the recovery process, click the wand icon to activate the SecureRecovery for Access Wizard. You can also access the tool by opening the View menu and selecting Switch to Wizard.
- Once you’ve located your corrupt Access file, click Next.
Step 5: Start the Recovery Process
- The selected Access files are added to a list. You also have the option to select other damaged files or folders by clicking Add files or Add folders. When enabled, Auto detect finds corrupted files for potential repair and restoration.
- Click Remove Files and Next if you accidentally add the wrong file.
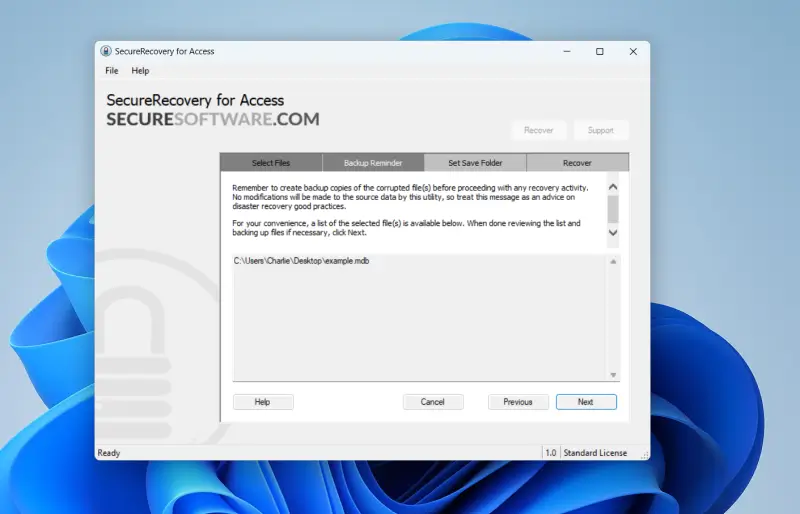
Step 6: Back Up Your Access Files
- Save your files to an external device or cloud backup services, even if they are damaged and inaccessible. When files are corrupted, there is a risk that recovery efforts could result in further data loss or damage. Even corrupted backups allow for additional recovery attempts.
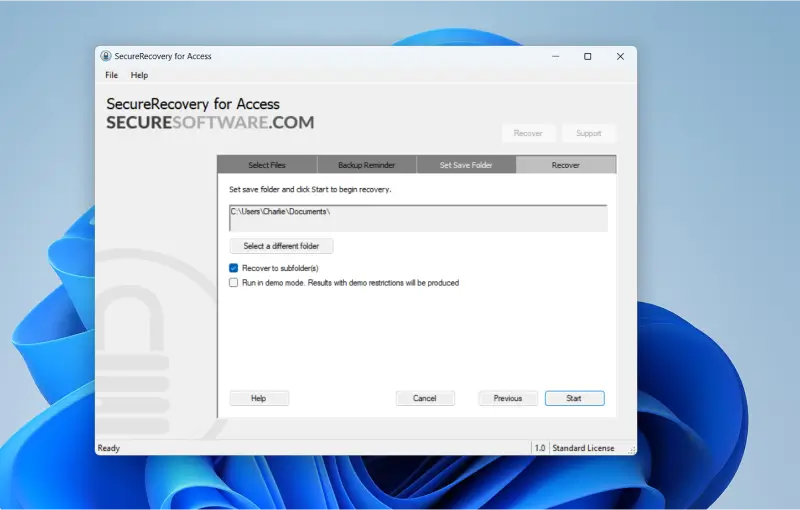
Step 7: Set Save Folder
- Choose the destination folder for restored MS Access files. The default path is C:\Users\Name\Documents. Name is a placeholder for the specific Windows profile. However, you can choose to save the files wherever you want by clicking Select a different folder.
- You can also run SecureRecovery for Access in demonstration mode to preview recoverable data, but this configuration comes with restrictions.
- Click Start to begin.
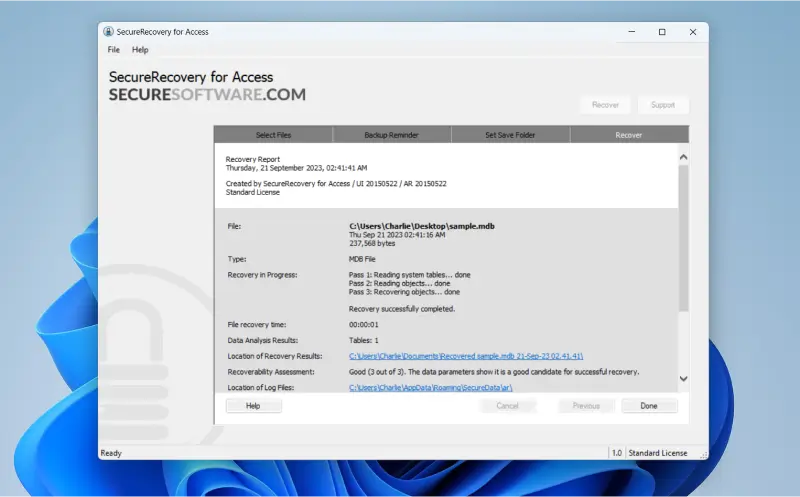
Step 8: Recovery Report
- A log and report will be generated. It highlights each step of the process and shows the success of repairs and recoveries.
Congratulations! Your corrupted Access files should be restored.
A “Sorry, No Data to Recover Detected” message in SecureRecovery for Access indicates that the file could not be repaired. However, that does not mean the file is lost. If the software does not repair and restore corrupted files, professional data recovery services can often utilize advanced tools and techniques to recover data in Access.
Frequently Asked Questions
What is a corrupted file?
A corrupted file is a damaged collection of digital data on a storage device. Corruption occurs for various reasons, including hardware failure, malware infections, software glitches, and unexpected interruptions while recording data. Regardless, the result is the same. The file is unreadable. Files often corrupt without warning, which reinforces the importance of regular backups.
What are some symptoms of a corrupted Access file?
The first sign is that the file will not open. Microsoft may alert you if it detects damage, and you could receive an error that the database format is not recognized.
Is backing up important?
Yes. Backups are an essential practice when storing sensitive information. Ideally, you should have several copies of valuable files to protect against data loss from a ransomware incident or natural disaster. If you only have local backups, they could also be exposed to the same damage or infection as your primary device. Even if you experience file corruption, creating backups of existing data can be worthwhile, as they enable multiple recovery attempts.